Remote Triggers for the Bash Bunny Mark II
One of the greatest new features of the Bash Bunny Mark II is remote triggers. With this, a payload — or multiple stages of a payload — can be triggered from afar. These can be done with any bluetooth low-energy device, including most smartphones. In this article I’ll demonstrate how to use this handy new feature.

THE SCENARIO
Imagine a social engineering engagement where the target is asked to print a document from a flash drive. The Bash Bunny, with ATTACKMODE STORAGE, will present itself as just such a benign device in the first stage of an attack. Then the opportunity presents itself to launch a second stage — emulating a HID device and performing keystroke injection — when the target turns their back to fetch the printout.
THE CODE
# # Remote Trigger for Bash Bunny Mark II Example # LED SETUP # # Stage 1: Benign flash drive # ATTACKMODE STORAGE LED STAGE1 WAIT_FOR_PRESENT myphone # # Stage 2: Evil keystroke injection attack # ATTACKMODE STORAGE HID LED STAGE2 QUACK GUI r QUACK DELAY 200 QUACK STRING cmd /k tree c:\ QUACK ENTER
PULLING OFF THE ATTACK
For this attack to proceed to the second stage, you simply need to advertise the BLE device named “myphone”. This can either be the name of a BLE device that advertises whenever it’s on — like a bluetooth speaker — or advertisements specifically sent from an app like BLE Tool.
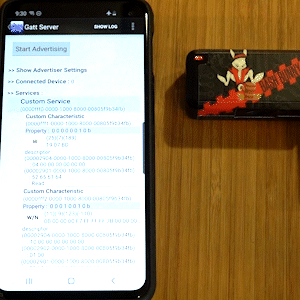
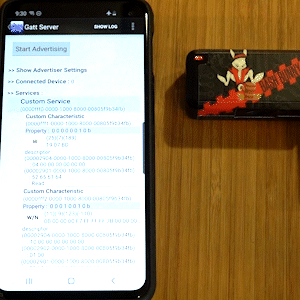
CONFIGURING BLE TOOL
Any bluetooth utility capable of broadcasting BLE advertisements will work. In testing I often times find myself using the highly configurable and aptly named BLE Tool for Android. If you choose to test with it, there are only 3 steps to follow:
- Tap GATT Server
- Specify a device name from the Advertiser settings (under the […] menu)
- Tap Start Advertising
HOW REMOTE TRIGGERS WORK
The WAIT_FOR_PRESENT and WAIT_FOR_NOT_PRESENT extensions work by setting the BLE module to Observation mode (AT+ROLE=2), then continuously saving the scanned airwaves to a temporary file on a 5 second interval (timeout 5s cat /dev/ttyS1 > /tmp/bt_observation). That binary file is then checked for the string value specified with the extension (grep -qao $1 /tmp/bt_observation).
If you’re curious what other advertisements might be found, consider running strings against this file while in observation mode. For faster remote triggers, consider modifying the extension for shorter scan durations.